Is Your Toolbelt Ready for Spring4Shell? Here it Comes

Are You Prepared for Spring4Shell? Guess What, it’s Here!
The Log4j vulnerability (CVE-2021-44228 aka Log4Shell) *was* the hottest topic in security. Now it’s Spring4Shell (CVE-2022-22965). Although the news cycle will keep moving on, the lingering effects of this vulnerability, like others before it, live on for years. Vulnerabilities like these are already endemic in the software supply chain due to its use in so many diverse software products, commercial and open source. Because of this, it’s critical that security professionals focus both on a timely response now and take a long haul approach, since it won’t be possible to plug all the log4j vulnerabilities in a day, week, or month.
A House Isn’t Built in Day
Application security engineers need to play the long game with black swan events like log4j and Spring4Shell. Take Heartbleed, for example. It was discovered nine years ago yet still has consequences today. Every zero-day vulnerability becomes an N-day vulnerability tainting the software supply chain from that point forward. Patching your software and all your application dependencies, a formidable job already, doesn’t mean log4j vulnerabilities won’t rear their heads in future software reuse, acquisitions, or dependent services.
Consider the analogy of building a house: It requires a team of tradespeople, multiple tools, and an organized, well-defined approach. Each of the tools are needed, each has a defined purpose and plays a role in building that new house. Building a house requires knowledge and coordination between different trades. To build a house you need your trade skills, your people skills, and lots of tools—with a toolbelt to organize them.
A house isn’t built in a day, nor a week. It usually takes months from breaking ground to completion, assuming the availability of materials and tradespeople. Homes are never complete; repairs and renovations are as big a business as new home construction. Software, like houses, needs maintenance and upkeep. AppSec engineers and developers, just like tradespeople, need coordination and their toolbelt to bring together their tools.
Log4j won’t be gone in a few days or weeks. Reducing the risk to the enterprise will take months, and even then, the risk lingers in the software supply chain. ArmorCode application security posture management and DevSecOps orchestration is the toolbelt needed to tackle Log4Shell in a timely manner now and to maintain your response over time.
The Ongoing Log4Shell, Spring4Shell (and the next one) Challenge
Dealing with a significant and pervasive threat like Log4Shell or Spring4Shell is a challenge in terms of information gathering and analysis but also one of managing compliance, resources, processes, and workflows:
- Lack of visibility into application inventory and the ability to filter the overwhelming number of Spring4Shell vulnerability findings and alerts
- Managing the deployment and operation of numerous AppSec tools
- Dealing with the voluminous output of security findings, most of which are low-risk
- Maintaining a consistent, reliable audit trail of findings, remediation, and overall risk
- No system-of-record to account for applications in use
- AppSec bogged down by manual issue triaging and sifting through countless spreadsheets (this doesn’t scale or deliver the agility needed for DevSecOps to succeed)
- Antiquated traditional compliance tools and processes
- Compliance load takes engineers’ and developers’ time away from their critical job functions
- Multiple standards need to be met with steep penalties for non-compliance
- Slower compliance cycles unable to keep up with DevSecOps
This is a scary looking list of challenges, but it’s the reality faced by application security engineers daily. These aren’t specific to Log4j or Spring4Shell either, but the urgency and scale of these vulnerabilities increases the pain.
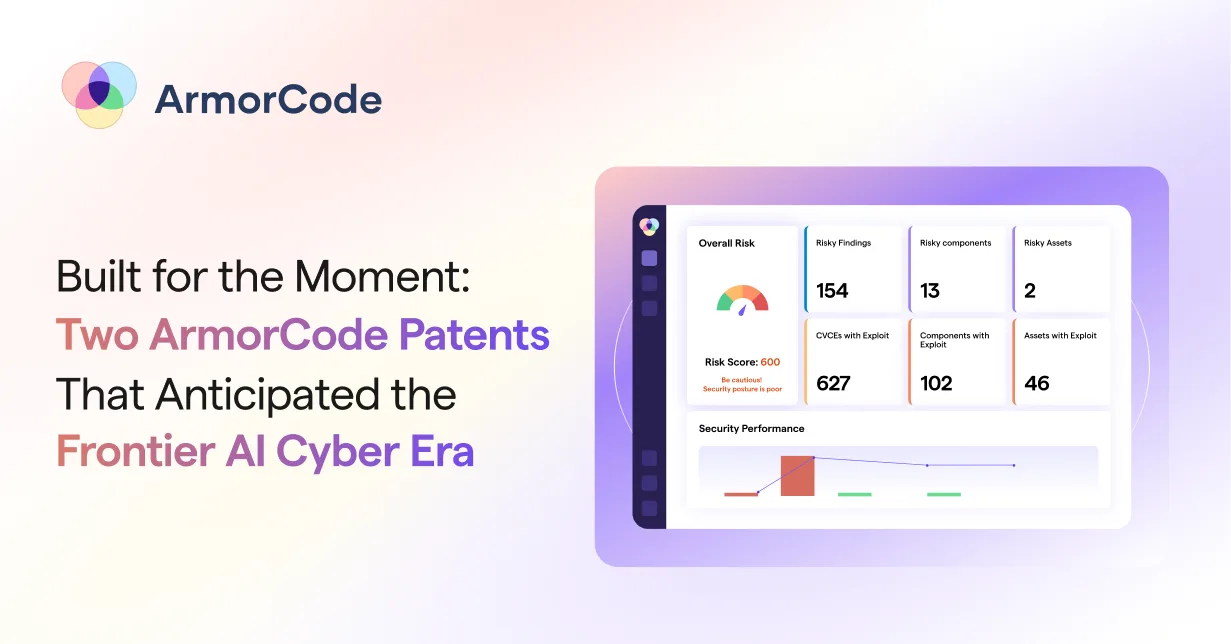
ArmorCode Is Your AppSec Toolbelt for Responding to Zero-Day Spring4Shell Vulnerabilities
Addressing Log4Shell and Spring4Shell vulnerabilities require various application security tools (SAST, DAST, IAST, etc.) and a litany of specific scanners. Software composition analysis (SCA) plays an important role in detecting the vulnerability in acquired software and software bill of materials (SBOMs) should be reporting the presence of the Log4j and Spring4Shell packages. The tools and associated processes create a lot of information, overwhelmingly so. Orchestrating and managing all of this is the role of your toolbelt.
The ArmorCode AppSecOps platform is the toolbelt for the AppSec practice, providing a single platform for managing your entire response to Log4Shell- or Spring4Shell vulnerabilities.
Centralize All Findings and Remediations
The ArmorCode platform centralizes all Spring4Shell and Log4j (and other) vulnerability findings and remediations from AppSec tools: including SAST, DAST, SCA, bug bounties, pen testing, and more. Findings are normalized, duplicates are removed and are correlated and prioritized—focusing AppSec resources where they are needed most. ArmorCode maintains a “system of record” for all applications and the security findings and both a point-in-time and trend analysis of security risk per application.
Centralizing, organizing and managing all your findings reclaims time wasted in tool operation, collecting and sifting through tool output, and back-and-forth debates between development and AppSec engineers. Issues can be triaged in a fraction of the time. Prioritization of risks means your limited resources are deployed to solve the highest risks, based on business value.
New applications can be onboarded into the application security framework in minutes, not days, and the risk of black swan events like Log4Shell or Spring4Shell can be managed in real-time.
Orchestrate the DevSecOps Pipeline Response
Orchestrating the DevSecOps pipeline is critical in removing the manual processes that slow down the response to security events like Log4Shell. It’s also critical to automate as much as possible the integration of many tools and sources of feedback into the process.
ArmorCode orchestrates DevSecOps eliminating manual processes by integrating and automating the intersection of AppSec tools and DevSecOps. Over 80 built-in integrations are already available and new ones are continuously being added. The platform maintains a knowledge base (KB) of security research that is specific to the policies and priorities of the organization to enforce security controls within the development processes. An audit trail of security findings and disposition is maintained throughout the SDLC.
Coordination of developers and AppSec is critical to an efficient response. The ArmorCode platform integrates with DevSecOps orchestration and issue management tools like Jira and communication tools like Slack to facilitate collaboration between AppSec and development teams. For example, as tickets are created in Jira for the development team they are appended with linked articles from ArmorCode’s knowledgebase to help quickly remediate issues.
Automate Continuous Compliance
Vulnerabilities like Log4Shell and Spring4Shell have a major impact on compliance. Public companies in particular are responsible for maintaining sufficient security posture, and the SEC has already brought enforcement actions against companies failing to comply. Black Swan events create greater strain on the compliance team. Being well-funded and prepared is essential for maintaining compliance.
The ArmorCode Platform helps your compliance program keep pace with your software releases by enabling automatic application evaluation against compliance standards including SOC2, GDPR, FedRAMP, HIPAA, and OWASP Top 10. Compliance is monitored and maintained on a continuous and automatic evaluation of security posture against key standards. This provides real-time risk assessment and on-demand compliance reporting. Customized controls provide flexibility to meet internal audit control requirements as needed.
Preparing for the Next Zero Day Event
A house isn’t built in a day, but it’s also never completely finished when you consider long term maintenance, repairs and renovations (home improvement is a $464 billion market!) Extending this analogy to software security, it’s essential to respond quickly to vulnerabilities and exploits, but equally important to maintain and improve your security posture for the next security crisis.