Top 5 Organizational Application Security Challenges

Application security has never been more complex; nor will it ever be as simple as it is now. Developers are under pressure to do more from a security standpoint, and security teams face a challenge in broadening attack vectors and surfaces. As DevSecOps continues to mature, organizations are trying to determine the best ways to approach the challenges of application security . In this post, we’ll take a look at the top AppSec issues plaguing businesses, and what can be done to help address these pain points.
1. Scaling challenges in a dynamic threat landscape
“Tools do not make software secure! They help scale the process and help enforce policy.” Michael Howard, 2006 OWASP AppSec Conference
Software security does not exist in silos. Infrastructure changes impact applications, and application decisions have an impact on infrastructure. As the number of apps, resulting infrastructure, and cloud security tools within an organization increases, so too does the complexity of managing software security, particularly if AppSec programs haven’t been built with scaling (and cloud) in mind. As new and unforeseen security issues emerge daily, this compounds the complexity of management.
With each new database call or each new open-source library you use, there will be extra security overheads. Eventually, the number of alerts can become overwhelming and impossible to untangle. While each individual scanning tool may bring in new security information, it also brings headaches for security teams as they must manually correlate issues across tools. The orchestration of security activities from a wider perspective is critical for scaling, especially as asset lists and dependencies grow.
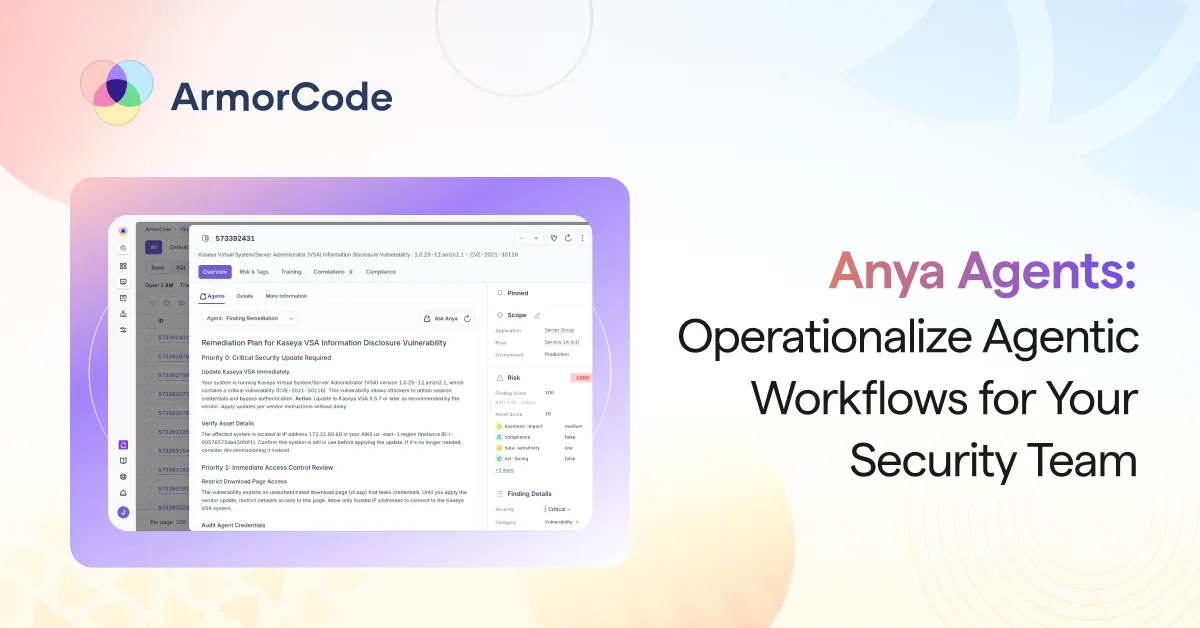
To be able to scale while minimizing any compounding effects in the technical overheads of security management requires a holistic perspective, and at times, re-architecture of asset and code security management. An Application Security Orchestration and Correlation (ASOC) tool or an AppSecOps solution to automate workflows and correlate data across AppSec sources and provide a unified remediation jump-off point, becomes not just a desirable solution, but a critical one to address the business need.
Learn how a financial technology company with hundreds of microservices and apps reduced time spent in manual product security activities with ArmorCode, to scale its growing list of compliance-heavy services.
2. Lack of DevOps workflow integration
“Just 23% of teams put SAST lite scanners in a web IDE” – Gitlab 2021 DevSecOps Survey Results
For much of the industry, AppSec tools have been add-ons to specific phases within the DevOps pipeline. But these tools, like Software Composition Analysis and Static Application Security Testing, weren’t built with DevOps in mind, to integrate directly into the CI/CD process. Plugins or automated triggers beyond what DevSecOps team members develop internally may be limited and/or only reflect certain states of systems. Each tool often lives in a silo, and doesn’t interoperate with other tools at other stages of the SDLC. As a result, security teams often send issues that lack context or duplicative tickets to developers, causing friction and a lack of action in fixing the right security holes. When security testing and reporting isn’t triaged and integrated into developer environments, vulnerabilities can slip through the cracks or get overlooked by accident.
There is immediacy in security and compliance and their associated prioritization activities, and a need for it to be cloud-native and configured with developers in mind. This often becomes impossible to manage through existing people, processes, and technology alone. A new solution is needed that fits natively into security and developer workflows to prioritize vulnerabilities, automate remediation tasks, make suggestions to stakeholders where necessary, and measure security performance.
3. Skill set shortages
There is a global cybersecurity workforce gap of 3.4 million people – (ISC)² Cybersecurity Workforce Study, 2021
Hiring and retaining experienced security personnel has never been harder. Thanks to a tight niche job market and employee expectations, skills shortages are widespread. Without more people on the ground, how can organizations run effective AppSec programs? The answer is that they often can’t. Overworked employees spend time jumping between tools doing manual reviews and reporting, creating bottlenecks that frustrate other stakeholders. Teams get buried in an avalanche of alerts, and errors and oversights occur. Attempting to scale development operations compounds these issues.
To combat an internal skills shortage, there are a number of ways that you can approach the problem. Outsourcing, particularly in conducting a regular Application Security Risk Assessment (ASRA), remains popular. However, businesses are realizing the value of integrated solutions that provide real-time Application Security management functionality and views for AppSec teams, developers, and management. Building on internal processes, you can effectively bring to life real-time Application Security Risk Assessment, running scheduled or on-demand what-if risk scenarios to determine impacts and mitigations. Automation not only buys time, but it frees up knowledgeable personnel to work and build on unique problems, rather than ones that are similar to past problems.
4. Balancing speed and security
>63% of Respondents agree “Shipping fast takes priority over shipping secure.”, State of Application Security Operations 2022, ArmorCode
What’s more important? Shipping fast or shipping securely? And do they really have to be in conflict? While Deployment Frequency and Time to Release are key focuses for management, the focus must also be on metrics like the number of Critical or High Severity Vulnerabilities in Production Code. Can weekly releases really have the same degree of security scrutiny as bi-monthly releases? The answer is yes – with the right practices and structure built into the CI/CD cycle. If your aim is to move to production faster while at the same time championing security, then an AppSecOps or DevSecOps orchestration solution will be a key tool in your tool belt.
By integrating, automating, and orchestrating AppSec practices and structure, security is managed repeatedly, just-in-time, and with a focus on dependencies. The right solution provides the ability to build on playbooks and guardrails as needs change, with the capability to drill-down, as well as provide two-way communication with tools like Jira to notify stakeholders in the systems they work within.
5. Application security in production code
“Shift left, shift right. What about shift everywhere?” – Paul Holland, Information Security Forum via Computer Weekly
A major application security challenge is not just in securing and monitoring applications before they hit production, but doing so in production, too. Cloud Security Posture Management (CSPM) works at the infrastructure level at runtime to identify misconfigurations in multi-service cloud workloads. Tools like Application Performance Monitoring and Runtime Application Self-Protection offer runtime security, but they do not directly tie in to development. So, is enough being done to manage AppSec at the application level from code to runtime? What if it’s across multiple clouds or regions? If a new change is pushed to production, do you have an immediate view of its security posture as it relates to other assets and services, and does it alert developers?
With all the focus on Shift Left, it’s now apparent there also needs to be an Extend Right, one that can alert developers to risks in production code, in their own tools. AppSec programs can now benefit from Application Security Posture Management (ASPM), a DevSecOps solution that stretches into production, to provide a view of security posture across APIs, data, services, dependencies, and more.
ArmorCode provides a single AppSecOps platform that unifies use cases across ASPM, vulnerability management, DevSecOps orchestration, and more to help organizations integrate application security across the CI/CD pipeline and into production. Talk to us about taking your DevSecOps to the next level.