What is Security Compliance?
Security compliance explained: frameworks, regulations, and best practices to reduce risk, build trust, and stay audit-ready year-round.
Table of Contents
Security compliance is the practice of adhering to regulatory standards, laws, and industry frameworks designed to protect sensitive data and ensure the integrity of digital systems.
Historically, organizations viewed compliance as a “checkbox exercise”—an annual disruption where teams scrambled to generate reports for auditors. However, in today’s digital-first economy, compliance has evolved. It is no longer just a legal requirement; it is a business enabler that builds customer trust and opens new markets.
For modern enterprises utilizing DevSecOps, the goal has shifted from “Point-in-Time Compliance” (passing an audit once a year) to “Continuous Compliance”—maintaining a secure, audit-ready posture 24/7/365 across the entire software development lifecycle (SDLC).
What is Security Compliance?
Security compliance is the ongoing process of meeting the security requirements established by laws, regulations, industry standards, and contractual obligations. It encompasses the policies, procedures, technical controls, and documentation that organizations implement to demonstrate they are protecting data and systems according to defined standards.
Compliance requires organizations to maintain security controls, regularly assess their effectiveness, document evidence of compliance, and adapt to evolving requirements over time. From protecting customer financial data to securing healthcare information to ensuring the safety of digital products, compliance has become a business imperative that touches every aspect of how organizations build and operate software.
Security compliance typically involves three core elements:
Controls: The technical and administrative safeguards implemented to protect systems and data. Examples include access controls, encryption, vulnerability management, and incident response procedures.
Evidence: Documentation and audit trails that prove controls are in place and operating effectively. This includes policies, logs, scan reports, remediation records, and attestations.
Governance: The organizational structures, processes, and accountability mechanisms that ensure compliance is maintained. This includes roles and responsibilities, review cycles, exception management, and reporting.
Why is Security Compliance Important?
Security compliance serves multiple critical functions beyond simply avoiding regulatory penalties.
Regulatory Mandate
Many industries are subject to mandatory compliance requirements. Financial services organizations must comply with PCI DSS for payment card data. Healthcare organizations in the US must meet HIPAA requirements. Organizations selling digital products in the EU will soon need to comply with the Cyber Resilience Act (CRA). Non-compliance can result in significant fines, legal action, and operational restrictions.
Customer Trust
Compliance certifications such as SOC 2, ISO 27001, and FedRAMP signal to customers that an organization takes security seriously. In competitive markets, demonstrating compliance can be a differentiator that accelerates sales cycles and opens doors to security-conscious enterprise customers.
Risk Reduction
Compliance frameworks are built on security best practices developed by experts over years of experience. By implementing the controls required for compliance, organizations systematically reduce their attack surface and improve their security posture. The structure and rigor of compliance programs often surface security gaps that might otherwise go unnoticed.
Operational Discipline
The processes required for compliance—regular assessments, documented procedures, audit trails, exception management—create operational discipline that benefits the entire organization. This discipline extends beyond security to improve overall software quality and organizational maturity.
Business Enablement
Many enterprise contracts require vendors to demonstrate compliance with specific frameworks. Government contracts often mandate FedRAMP or CMMC compliance. Healthcare customers require HIPAA compliance from their vendors. Achieving and maintaining compliance opens market opportunities that would otherwise be inaccessible.
Common Security Compliance Frameworks and Regulations
The compliance landscape includes a mix of mandatory regulations and voluntary frameworks. Understanding the key frameworks helps organizations prioritize their compliance efforts.
Regulatory Requirements
EU Cyber Resilience Act (CRA): Forthcoming EU regulation establishing mandatory cybersecurity requirements for products with digital elements sold in the EU market. The CRA requires secure-by-design development, vulnerability management, incident reporting, and product lifecycle security. Perhaps most important to manufacturers and product teams, the CRA features a 24-hour vulnerability reporting requirement under Article 14 for actively exploited vulnerabilities. Learn more about CRA requirements.
DORA (Digital Operational Resilience Act): EU regulation establishing mandatory ICT risk management and operational resilience requirements for financial entities, including banks, insurers, investment firms, and payment service providers, as well as their critical third-party ICT providers. DORA requires comprehensive ICT risk management frameworks, incident classification and reporting, regular digital operational resilience testing, and rigorous third-party risk management for technology vendors. The regulation became applicable in January 2025.
PCI DSS (Payment Card Industry Data Security Standard): Applies to any organization that processes, stores, or transmits payment card data. PCI DSS specifies technical and operational requirements for protecting cardholder data, including network security, access controls, vulnerability management, and regular testing.
HIPAA (Health Insurance Portability and Accountability Act): US regulation governing the protection of protected health information (PHI). HIPAA’s Security Rule establishes administrative, physical, and technical safeguards that covered entities and business associates must implement to protect electronic PHI.
GDPR (General Data Protection Regulation): EU regulation governing the collection, processing, and protection of personal data for EU residents. GDPR establishes requirements for data protection by design, breach notification, data subject rights, and cross-border data transfers.
SOX (Sarbanes-Oxley Act): US regulation requiring publicly traded companies to implement internal controls over financial reporting. For technology organizations, SOX compliance typically involves controls over systems that process financial data, including access management, change management, and audit logging.
Industry Frameworks
SOC 2 (System and Organization Controls 2): A widely adopted framework for service organizations, SOC 2 evaluates controls related to security, availability, processing integrity, confidentiality, and privacy. SOC 2 reports are commonly required by enterprise customers evaluating SaaS vendors.
ISO 27001: An international standard for information security management systems (ISMS). ISO 27001 certification demonstrates that an organization has established a systematic approach to managing information security risks. The framework is widely recognized globally and often required for international business.
NIST Cybersecurity Framework (CSF): A voluntary framework developed by the US National Institute of Standards and Technology that provides guidance for managing cybersecurity risk. NIST CSF is widely adopted across industries and forms the basis for many sector-specific requirements.
NIST SP 800-53: A comprehensive catalog of security and privacy controls for federal information systems. While mandatory for US federal agencies, NIST 800-53 is also widely adopted by private sector organizations seeking a rigorous control framework.
CIS Controls: A prioritized set of actions developed by the Center for Internet Security that provides specific guidance for defending against common cyber attacks. The CIS Controls are often used as a practical implementation guide alongside broader frameworks.
FedRAMP (Federal Risk and Authorization Management Program): A US government program that provides a standardized approach to security assessment, authorization, and continuous monitoring for cloud products and services used by federal agencies.
CMMC (Cybersecurity Maturity Model Certification): A framework required for organizations in the US defense industrial base. CMMC establishes tiered security requirements based on the sensitivity of the information being protected.
Industry-Specific Standards
OWASP (Open Web Application Security Project): While not a compliance framework per se, OWASP standards like the OWASP Top 10 and OWASP ASVS are commonly referenced in compliance requirements for application security. Many regulations and frameworks require addressing OWASP-identified vulnerabilities.
HITRUST CSF: A certifiable framework that harmonizes requirements from multiple regulations and standards relevant to healthcare, including HIPAA, PCI DSS, and NIST. HITRUST certification is increasingly required by healthcare organizations evaluating vendors.
The Challenges of Modern & Continuous Compliance Management
Organizations face significant challenges in achieving and maintaining compliance, particularly as application architectures, development practices, and regulatory requirements evolve.
Tool and Data Fragmentation
Modern organizations use dozens of security tools across application security testing, cloud security, infrastructure vulnerability scanning, and more. Compliance evidence is scattered across these disconnected systems, making it difficult to get a unified view of compliance posture or efficiently gather evidence for audits.
This fragmentation has driven the emergence of Application Security Posture Management (ASPM) and Unified Exposure Management platforms that aggregate and normalize findings across security tools. By consolidating application, cloud, and infrastructure security data into a single view, these platforms provide the foundation for continuous compliance by replacing manual evidence gathering with automated collection and enabling real-time compliance posture visibility across frameworks.
Manual Evidence Collection
Many organizations still rely on spreadsheets, emails, and manual processes to track compliance status and collect audit evidence. This approach is time-consuming, error-prone, and difficult to scale. Security teams spend excessive time on administrative tasks rather than addressing actual security issues.
Evolving Requirements
Compliance is not static. Regulations change, new frameworks emerge, and existing standards are updated. Organizations must continuously monitor regulatory developments and adjust their programs accordingly. The recent introduction of the EU Cyber Resilience Act (CRA) is just one example of how the compliance landscape continues to expand.
Audit Preparedness
Traditional approaches to compliance treat audits as periodic events requiring intensive preparation. Teams scramble to gather evidence, close gaps, and document controls in the weeks before an audit. This reactive approach creates stress, diverts resources, and often reveals issues too late to address properly.
Exception Management
No organization achieves perfect compliance. Business requirements sometimes conflict with security controls, legacy systems may not support required configurations, and risk-based decisions must be made. Managing these exceptions—documenting justifications, implementing compensating controls, tracking expiration dates, obtaining approvals—requires structured processes that many organizations lack.
Cross-Team Coordination
Compliance is not solely a security function. It requires coordination across development, operations, legal, and business teams. Aligning these stakeholders, establishing clear ownership, and maintaining consistent processes across organizational boundaries is a persistent challenge.
Security Compliance Best Practices
Organizations that successfully manage compliance share common practices that transform compliance from a burden into a sustainable capability.
Automate Evidence Collection
Replace manual evidence gathering with automated processes that continuously collect and organize compliance evidence. Integration with security tools, development pipelines, and operational systems enables real-time evidence collection without manual intervention. This automation not only saves time but also improves evidence quality and completeness.
Implement Continuous Compliance
Shift from periodic compliance assessments to continuous monitoring. Real-time dashboards that track control effectiveness, identify gaps, and alert on compliance drift enable organizations to maintain a compliance posture rather than periodically scrambling to achieve it. Continuous compliance also supports more frequent and less disruptive audits.
Organizations adopting Continuous Threat Exposure Management (CTEM) programs find natural alignment here—CTEM’s five-stage cycle of scoping the exposure surface, discovering risks, prioritizing based on business context, validating exploitability, and mobilizing remediation directly supports the evidence collection and control validation that compliance requires.
Map Controls Across Frameworks
Many compliance frameworks share common requirements. Organizations subject to multiple frameworks should map controls to identify overlaps and implement unified controls that satisfy multiple requirements simultaneously. This approach, sometimes called a “comply once, certify many” strategy, reduces duplication and improves efficiency.
Integrate Compliance into Development
Embed compliance requirements into the software development lifecycle rather than treating compliance as a separate, downstream activity. Security testing integrated into CI/CD pipelines, automated policy checks, and developer guardrails help ensure that compliance issues and risks from AI-generated code are identified and addressed early when they are easiest and cheapest to fix.
Establish Structured Exception Management
Create formal processes for managing exceptions to compliance requirements. This includes documenting the business justification, identifying compensating controls, obtaining appropriate approvals, setting expiration dates, and tracking exceptions through resolution. A risk register or similar mechanism provides visibility into accepted risks.
Maintain Audit-Ready Documentation
Treat documentation as a continuous practice rather than an audit preparation activity. Policies should be current and accessible, procedures should reflect actual practices, and evidence should be organized and retrievable. When audit-readiness is the steady state, audits become validation exercises rather than fire drills.
Leverage Risk-Based Prioritization
Not all compliance gaps carry equal risk. Relying on CVSS scores alone is insufficient for business-normalized prioritization. As such, focus remediation efforts on the gaps that pose the greatest risk to the organization, considering factors like data sensitivity, exploitability, and business impact. Risk-based prioritization ensures that limited resources are applied where they matter most.
Compliance vs. Security: Understanding the Difference
While compliance and security are related, they are not synonymous. Understanding the distinction helps organizations build programs that achieve both compliance and genuine security.
Compliance is a baseline. Compliance frameworks establish minimum requirements that organizations must meet. Achieving compliance means meeting these minimum requirements, but it does not guarantee security. Compliance requirements often lag behind emerging threats, and frameworks cannot anticipate every attack vector.
Security is the goal. Security is the ongoing practice of protecting systems, data, and users from threats. Effective security programs go beyond compliance requirements to address organization-specific risks, emerging threats, and continuous improvement.
Compliance provides structure. For organizations building security programs, compliance frameworks provide a structured starting point. They codify security best practices, establish clear requirements, and provide external validation through audits and certifications.
Security provides substance. Compliance without genuine security is checkbox compliance—meeting the letter of requirements without achieving the intended protection. Organizations should use compliance requirements as a foundation while building security programs that address their actual risk landscape.
The most effective enterprises treat compliance as one input to their security program, not the entirety of it. They implement controls that satisfy compliance requirements while also addressing risks that frameworks may not cover.
Building a Sustainable Compliance Program
A sustainable compliance program balances rigor with efficiency, enabling organizations to maintain compliance without excessive overhead.
Establish Governance
Define clear ownership and accountability for compliance. This includes executive sponsorship, cross-functional steering committees, and clear assignment of control ownership. Governance structures should include regular review cycles, escalation paths, and reporting mechanisms.
Assess Current State
Conduct a thorough assessment of the current compliance posture against applicable frameworks. Identify gaps between current practices and requirements, prioritize gaps based on risk, and develop a remediation roadmap. This baseline assessment provides the foundation for improvement.
Implement Controls
Deploy the technical and administrative controls required by applicable frameworks. Prioritize controls that address the highest-risk gaps and that satisfy requirements across multiple frameworks. Ensure controls are documented, tested, and monitored.
Automate Where Possible
Identify opportunities to automate compliance activities, including evidence collection, control testing, policy enforcement, and reporting. Automation improves efficiency, reduces errors, and enables continuous compliance. Platforms that unify security findings and automate workflows are particularly valuable.
Monitor and Measure
Implement continuous monitoring of compliance posture. Track key metrics like control effectiveness, remediation SLA adherence, exception status, and audit findings over time. Use dashboards and reports to maintain visibility and identify trends.
Prepare for Audits
Maintain audit-ready documentation and evidence throughout the year. Conduct internal assessments using the same criteria that external auditors will apply. Address identified issues proactively rather than waiting for audit findings.
Improve Continuously
Treat compliance as a journey rather than a destination. Learn from audit findings, security incidents, and near-misses. Update controls and processes as requirements evolve and as the organization matures. Benchmark against peers and industry best practices.
Achieve Continuous Compliance with ArmorCode
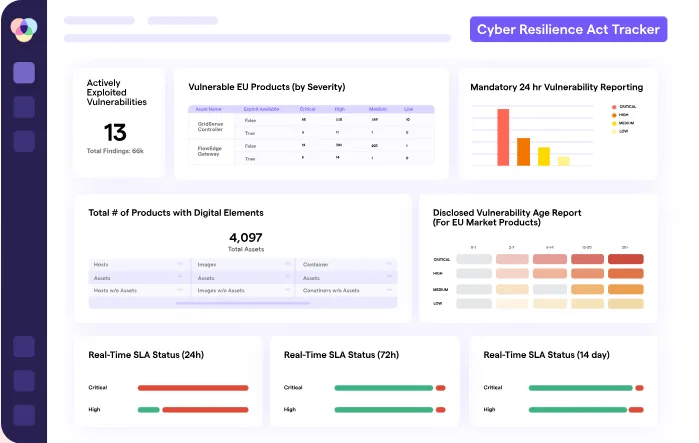
ArmorCode transforms compliance from a manual, reactive burden into an automated, continuous practice. ArmorCode unifies security findings across your applications, cloud, infrastructure, and AI. This enables ArmorCode to provide real-time visibility into compliance posture and automates the evidence collection and reporting that auditors require.
Unified Visibility: Consolidating findings from 325+ security tools into a centralized view of your compliance posture across frameworks with real-time dashboards that track control status, identify gaps, and demonstrate audit readiness.
Automated Evidence Collection: Replace manual evidence gathering with AI-powered automated processes that continuously collect and organize compliance evidence from all your integrated tools along with Anya, an agentic AI virtual security champion who can answer any natural-language compliance-related queries against your findings and data.
Structured Exceptions Management: Manage compliance exceptions with formal workflows, approvals, and audit trails that ensure accountability and policy alignment.
Audit-Ready Reporting: Generate customizable compliance reports that demonstrate control effectiveness, SLA adherence, and remediation progress to auditors and stakeholders.
Integration with DevSecOps: Embed compliance requirements into development workflows with automated policy checks and guardrails that identify compliance issues early in the development lifecycle along with identifying AI-generated code compliance risks.
ArmorCode helps organizations achieve compliance efficiently while building genuine security—ensuring that compliance programs deliver the protection they’re designed to provide.See how leading enterprises maintain continuous compliance with ArmorCode. Schedule a demo or take a tour today.