What is Exposure Management? The Complete Guide for 2026
A guide to understanding the modern security discipline that goes beyond vulnerability management, and why it matters for every enterprise security team.
The Evolution of Cyber Risk
Cybersecurity has fundamentally shifted from a reactive discipline to a proactive one, and exposure management sits at the center of that change. The way enterprises measure and manage cybersecurity risk is being rewritten in real time, driven by an attack surface that no longer fits the assumptions legacy programs were built on.
For decades, security teams operated on a predictable rhythm: scan periodically, score findings by CVSS, patch the highest numbers, and move on. That model assumed a bounded attack surface, a manageable toolset, and a clear line between a technical finding and business risk. None of those assumptions holds anymore.
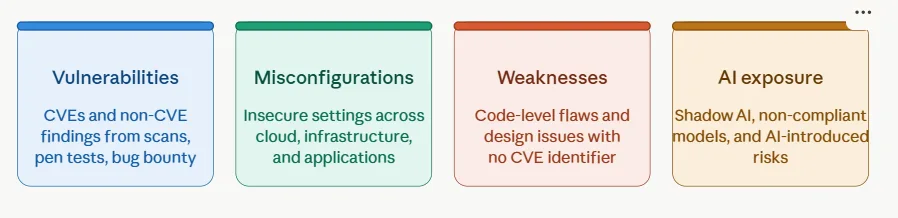
Today’s enterprise attack surface stretches across hybrid cloud workloads that spin up and down in minutes, hundreds of open-source dependencies pulled in by every build, AI models deployed faster than security teams can inventory them, and continuous code shipping from distributed development teams. New CVEs are disclosed daily, but CVEs are only one slice of the exposure picture. Misconfigurations, design weaknesses, identity issues, and shadow AI deployments rarely show up in a traditional scan, yet they are exactly where sophisticated attackers look first.
Exposure management cybersecurity programs are built for this reality. Not a tool category, not a vendor pitch, but a practice: a continuous, structured approach to understanding and reducing security risk across the entire enterprise.
The Expanding Attack Surface
The traditional IT asset inventory, a list of servers, endpoints, and known applications, no longer captures the full picture of organizational risk. Ephemeral cloud workloads, third-party SaaS, microservices, software supply chains, and AI agents have all become part of the modern attack surface, and most of them sit outside the visibility of legacy asset management tools. Add to this the volume problem: the rate of new CVE disclosures keeps climbing year over year, and that is before factoring in non-CVE exposures like cloud misconfigurations or AI-introduced risks.
The result is an attack surface that is dynamic, distributed, and expanding faster than any single tool or team can track. Periodic scanning misses things that appear and disappear between scan windows. Static asset inventories miss workloads that were never registered in the first place. And CVE-focused programs miss the entire categories of risk that attackers increasingly exploit.
The Problem with Traditional Vulnerability Management
Traditional vulnerability management was built for a simpler attack surface. It optimized for one job: finding known software flaws and ranking them by technical severity. That job still matters, but it has become a small fraction of what enterprise security teams actually need to do.
The deeper problem is what practitioners often call the reconciliation tax: the manual effort required to aggregate findings across fragmented tools, normalize them into a common language, deduplicate them, and figure out which ones actually matter. The average enterprise runs 45 or more security tools, each generating its own alert stream with its own scoring logic. Security teams end up spending more time toggling between dashboards and reconciling tool disagreements than they spend reducing actual risk. The findings pile up, the business context is missing, and what should be a clear signal becomes prioritization paralysis.
CVSS scores were never designed to answer the question that matters most: Is this exposure actually exploitable in our environment, and does it threaten anything our business cares about? Answering that question requires a different approach.
What is Exposure Management?
Exposure management is the continuous practice of identifying, analyzing, and prioritizing an organization’s security exposures across its full attack surface, including vulnerabilities, misconfigurations, unmanaged assets, code weaknesses, and AI risks, so that remediation efforts are directed at the risks most likely to be exploited and most likely to impact the business. It incorporates threat intelligence, asset criticality, and existing security control context to move organizations from reactive patching toward proactive, risk-based security operations.
The shift from CVSS scores to risk-based prioritization is the heart of the discipline. Exposure management is not a one-time scan or a quarterly assessment. It is a lifecycle that runs continuously, asking four ongoing questions: What are we exposed to? What actually matters right now? Is it truly exploitable here? Who fixes it, and how?
Key distinction: Exposure management is broader than vulnerability management. It includes CVE-based vulnerabilities, but also misconfigurations, code weaknesses, identity issues, supply chain risks, and AI exposure, and it extends the discipline from finding security issues to actively reducing the risk they represent.
Defining Exposure Management
The goal of enterprise security is not to generate more findings. It is to reduce exploitable risk; measurably, continuously, and in a way that aligns with how the business actually operates. That reframing is what separates exposure management from the practices that came before it. A traditional program counts vulnerabilities. A mature exposure management program measures and reduces real-world risk to the assets that matter most, the crown jewels that, if compromised, would meaningfully harm the business.
This is where threat intelligence, business impact, and reachability validation enter the picture. A critical CVSS score on an internal-only system that has no path to a crown-jewel asset is not the same risk as a medium-severity finding on an internet-facing service that handles customer data. Exposure management treats them differently because the business does.
Key Components of an Exposure Management Strategy
A mature exposure management strategy is built from five interconnected components, each feeding the next as part of a continuous cycle:
Asset discovery establishes the foundation. You cannot defend what you cannot see, and modern asset discovery has to extend beyond the data center to cover cloud workloads, containers, APIs, third-party services, and AI deployments. This is where the security posture conversation begins.
Vulnerability and exposure assessment brings in findings from every relevant source: SAST, DAST, SCA, cloud security posture management, infrastructure scanners, pen tests, bug bounty programs, and AI discovery tools. The goal here is breadth; capturing every category of exposure, not just the CVEs that show up in a single scanner.
Risk prioritization layers threat intelligence (EPSS scores, CISA KEV), asset criticality, business context, and reachability data on top of raw findings. This is where the noise gets filtered, and the signal emerges. It is also where attack paths come into view: the chains of weaknesses that, taken together, form an exploitable route to a high-value asset.
Validation confirms whether a finding is truly exploitable in your specific environment before remediation resources are mobilized. This step is what separates a theoretical risk from a real one, and it is where reachability analysis pays for itself.
Remediation workflows close the loop. Findings get routed to the right owner, with the right context, in the workflow they already live in. This is where many programs break down, and it is where the difference between a list of vulnerabilities and a meaningful reduction in cyber risk becomes most visible.
These five components are not a sequence to run once. They form a continuous cycle, with each pass through the loop tightening the organization’s overall risk posture.
Why Unified Exposure Management is the Future
Exposure management as a discipline has been understood for years. The gap has always been execution: the ability to actually operationalize it at enterprise scale, across the full breadth of the modern attack surface, with the speed and continuity that the threat landscape demands.
Unified Exposure Management (UEM) is the architecture that closes that gap.
UEM is not a product category. It is an approach: the practice of managing all exposure types (vulnerabilities, misconfigurations, weaknesses, and AI exposure) through a single, unified intelligence layer that connects to your existing security stack, normalizes findings across every source, and drives remediation through integrated workflows. The “unified” in UEM is the keyword. It refers to the unification of three things that have historically been fragmented:
- Visibility: a single, normalized view of exposures across all tools, teams, and domains, without requiring replacement of existing scanners or security investments.
- Prioritization: a shared risk language that layers threat intelligence, asset criticality, business impact, and reachability data into a single prioritized view, so every team, from developers to the board, is working from the same understanding of what matters most.
- Remediation: automated orchestration that routes findings to the right owner, in the right workflow, with the right context, so that the gap between discovery and fix closes as fast as the threat landscape demands.
Breaking Down Security Silos
Tool sprawl creates prioritization paralysis. When findings live in 12 different systems, each with its own scoring logic and its own dashboard, security teams spend their day toggling between consoles instead of fixing problems. AppSec, InfraSec, cloud security, and GRC each see their own slice of the picture, and no one sees the whole. The same vulnerability might be triaged six times across six different queues, or missed entirely because it falls between team boundaries.
Unified Exposure Management breaks this pattern by establishing what can be thought of as an enterprise exposure graph: a single, connected view of every asset, every finding, and every relationship between them. AppSec findings, infrastructure exposures, cloud misconfigurations, supply chain risks, and AI issues all live in the same intelligence layer, normalized to a common language and connected to the assets they affect. This is the single source of truth that fragmented programs lack, and it is the foundation that everything else, prioritization, validation, and mobilization, depends on.
The Role of Agentic AI in Prioritization
Agentic AI is changing how exposure management gets operationalized. Earlier generations of security AI were largely about telling: surfacing findings, generating reports, suggesting next steps. Agentic AI is about doing: correlating signals across domains, identifying toxic combinations (the intersection of a vulnerability, an over-privileged identity, and internet exposure), and automatically routing findings into the right remediation workflow.
ArmorCode’s agentic AI framework, Anya, sits at this layer. It correlates technical reachability with business criticality, so security teams stop chasing high-CVSS findings on assets that have no path to anything important. It surfaces toxic combinations as a single prioritized risk rather than three separate alerts in three different tools. And it automates the handoff to remediation, opening the right ticket in the right system with the right context, so the developer who has to fix it can act without leaving their IDE.
The shift this enables is significant. Rather than security teams triaging an endless queue of low-context alerts, agentic AI surfaces the small percentage of findings that represent real, immediate risk and moves them directly into the workflows where fixes happen.
The Forces Driving UEM Adoption
The shift toward UEM is being driven by three converging forces that show no signs of reversing.
The Regulatory Imperative: NIS2, DORA, the EU Cyber Resilience Act, and SEC disclosure rules are all moving in the same direction: organizations must demonstrate that they can operationalize risk reduction, not just report on it. Frameworks like Tiber-EU require security gaps to be closed in days, not months. The era of compliance-as-checkbox is over. Unified Exposure Management provides the continuous compliance posture that regulators now require: time-stamped audit trails, automated evidence collection, and regulatory framework mappings that are maintained continuously, not assembled manually in the weeks before an audit.
The Attack Surface Has Outgrown Point Tools: Cloud adoption, AI deployment, third-party dependencies, and distributed development have multiplied the number of exposure types and the speed at which new ones emerge. The enterprise attack surface is no longer a bounded, predictable perimeter. It is dynamic, distributed, and expanding continuously. Point tools, no matter how sophisticated in their individual domain, cannot provide the cross-domain correlation that modern exposure management requires. Enterprises have responded by adding more tools, which have created more alerts, more silos, and paradoxically, more coverage gaps. UEM inverts this dynamic. Rather than adding another tool to the stack, UEM becomes the intelligence layer that makes the existing stack coherent, normalizing, correlating, and prioritizing across every source without replacing any of them.
Security ROI Is Now a Board-Level Conversation: CISOs are under increasing pressure to demonstrate that security investment translates to measurable risk reduction. Tool sprawl makes this nearly impossible: when findings live in 12 different systems, ownership is unclear, and MTTR is tracked manually in spreadsheets, quantifying the impact of security investment is an exercise in estimation, not evidence. Unified Exposure Management creates the conditions for defensible ROI reporting: consolidated tool coverage, eliminated redundancies, measurable MTTR trends, and a single risk posture score that reflects real-world risk across the entire attack surface.
Why UEM is inevitable: The question for enterprise security teams is not whether to adopt a unified exposure management approach; it is when. The forces driving adoption (regulatory pressure, attack surface complexity, budget scrutiny) are structural and accelerating. Organizations that build a unified exposure management capability now will be positioned to meet the next wave of threats and compliance requirements without rebuilding their programs from scratch.
How ArmorCode Enables Unified Exposure Management
ArmorCode is built around the independent governance model: the idea that most enterprises already have the scanners and security tools they need, but lack the intelligence layer to make them work together. Rather than replacing existing tools, ArmorCode connects to 350+ of them, normalizes findings across every source, and takes over from there, prioritizing, validating, and remediating risk across applications, infrastructure, cloud, supply chain, and AI.
A Vendor-Agnostic Central Control Plane
ArmorCode’s value proposition starts with a deliberate architectural choice: it does not replace your scanners; it integrates with them. This vendor-agnostic, scanner-less design means there is no rip-and-replace, no vendor lock-in, and no abandoned investments. The tools your AppSec, infrastructure, cloud, and AI teams already rely on keep doing what they do best. ArmorCode becomes the intelligence layer that makes them coherent.
What makes this meaningful in practice is reachability. ArmorCode correlates findings across code, runtime, and network layers to validate whether an exposure is actually callable, reachable in production, and internet-facing, before it ever reaches a developer’s queue. This is how security teams move from managing thousands of findings to focusing on the small percentage that represent real, immediate risk.
The platform spans four integrated solutions, each sharing a unified asset model, a common risk scoring engine, and a single remediation workflow layer:
- Application Security Posture Management (ASPM) unifies AppSec findings from SAST, DAST, SCA, IaC scanning, and pen testing into a single prioritized view, correlated to the applications and services that matter most.
- Unified Vulnerability Management (UVM) extends the same approach across infrastructure, cloud, and the broader vulnerability landscape, replacing the fragmented dashboards of legacy RBVM with a single risk-based view.
- Software Supply Chain Security (SSCS) brings SBOM management, open-source risk, and software supply chain integrity into the same intelligence layer, so supply chain risk is part of the overall exposure picture, not a separate workstream.
- AI Exposure Management (AIEM) addresses the fastest-growing blind spot: shadow AI, non-compliant models, AI-introduced code weaknesses, and the new attack surface that AI agents and MCP servers introduce.
Together, these four solutions give security teams full-stack visibility from code to cloud to AI, without forcing them to abandon the tools they already trust.
Automating the Path to Remediation
Visibility and prioritization only matter if they translate into fixes. The last-mile breakdown, where findings stall because ownership is unclear, context is missing, or the workflow is broken, is what keeps MTTR measured in months instead of days.
This is where Anya, ArmorCode’s agentic AI framework, takes over. Anya pinpoints asset owners, opens the right ticket in the right system (Jira, ServiceNow, or whatever the team already uses), and delivers context-aware, role-specific guidance: detailed fix instructions for developers, prioritized remediation queues for AppSec leads, and risk posture summaries for security executives. The developer who has to fix the issue gets the context they need without leaving their IDE. The AppSec lead sees a prioritized burndown, not a flood of alerts. The CISO sees risk reduction, not raw vulnerability counts.
The result is a dramatic compression of the discovery-to-fix cycle. Findings that used to take weeks to route, contextualize, and close move through the system in hours, and the choke points that close the most attack paths get prioritized first.
Taking Control of Your Exposures
Exposure management is the shift from reactive patching to proactive risk reduction, from tool-centric fragmentation to unified intelligence, from drowning in alerts to acting on signal. The discipline is no longer optional. The attack surface is too large, the threat landscape too fast, and the regulatory pressure too sustained for the old model of periodic scanning and CVE counting to keep up.
Modern risk exposure management requires unified visibility, continuous monitoring, and automated remediation. The organizations getting this right share a few traits. They treat exposure management as a continuous practice, not a quarterly project. They cover the full attack surface, not just the parts a single scanner sees. They prioritize real-world risk, not raw severity scores. They invest in mobilization as seriously as identification. And they unify their existing security stack into a single intelligence layer rather than adding another point tool to the pile.
ArmorCode helps enterprise security teams remediate less and reduce risk faster by making the security stack you already own work as a coherent system. To see unified exposure management in action, take a tour of the ArmorCode Platform or request a demo.
Frequently Asked Questions
What is the difference between exposure management and vulnerability management?
Vulnerability management is a subset of exposure management. Vulnerability management focuses on identifying and remediating vulnerabilities in infrastructure, primarily CVE-based flaws in operating systems, network devices, and servers, through scanning, CVSS scoring, and patch prioritization. It is a core security practice, but its scope is limited to the infrastructure layer.
Exposure management is broader in scope. It covers the full range of exploitable risks across the modern attack surface, including vulnerabilities, misconfigurations, unmanaged assets, code weaknesses, and AI risks. It also incorporates threat intelligence, asset criticality, reachability validation, and business context into prioritization, and it extends through to remediation with automated owner assignment and workflow integration, so findings get closed rather than filed. In short, vulnerability management tells you what is vulnerable in your infrastructure. Exposure management tells you what is actually at risk across your entire attack surface and makes sure it gets fixed.
Why is unified exposure management better than using multiple point solutions?
Point solutions create the reconciliation tax: the manual effort to aggregate findings across fragmented tools, normalize them into a common language, deduplicate them, and figure out which ones actually matter. The average enterprise runs 45 or more security tools, each with its own dashboard and its own scoring logic, and security teams end up spending more time reconciling tool disagreements than reducing risk. The result is prioritization paralysis, alert fatigue, and a backlog that never burns down.
Unified Exposure Management eliminates this by bringing all exposure types into a single intelligence layer, with a shared risk language, automated correlation across domains, and integrated remediation workflows. A single pane of glass replaces a dozen dashboards, intelligent prioritization replaces severity-based queues, and automated mobilization replaces manual handoffs. The outcome is faster remediation, lower MTTR, and a defensible story about how security investment translates into measurable risk reduction.
How can organizations implement exposure management if they already have existing security tools?
Organizations do not need to rip-and-replace their existing security stack to implement exposure management. Vendor-agnostic platforms like ArmorCode are designed to integrate with the scanners and tools enterprises already rely on, ingesting findings from 350+ sources, normalizing them, and adding the intelligence layer that fragmented stacks are missing. This approach maximizes existing investments while adding unified visibility, risk-based prioritization, reachability validation, and automated remediation on top.
The practical path looks like this: keep your scanners, keep your cloud security tools, keep your pen test program, and layer a unified exposure management platform on top to correlate, prioritize, and orchestrate across all of them. Most enterprises see the biggest early wins in the mobilization stage, where automated owner assignment and contextual fix guidance compress MTTR almost immediately.


