Anthropic’s Claude Mythos and What it Means for Security

Last week, Anthropic announced Claude Mythos Preview and Project Glasswing, and the cybersecurity industry is still processing the implications. This is a technology leap that forces every security leader to recalibrate how they think about risk.
At ArmorCode, we’ve spent the past week talking with customers, partners, and analysts about what Mythos means for the enterprise. The short version: AI-powered vulnerability discovery at this scale is a genuine breakthrough, and it makes the operational discipline of prioritizing, triaging, and remediating vulnerabilities more important than ever before. Not less.
Let me explain.
What Are Claude Mythos Preview and Project Glasswing?
Claude Mythos Preview is a new frontier AI model from Anthropic. It’s a general-purpose model, not one specifically built for security. But during testing, Anthropic discovered it possesses striking cybersecurity capabilities that far exceed any prior model. In their own words, AI models have reached a level where they can surpass all but the most skilled humans at finding and exploiting software vulnerabilities.
The numbers speak for themselves. In pre-release testing, Mythos identified thousands of previously unknown zero-day vulnerabilities across every major operating system and every major web browser. It found flaws that had survived decades of human security review and millions of automated tests. It reproduced vulnerabilities and developed working exploits on the first attempt in over 83% of cases. In one documented instance, it uncovered a 27-year-old vulnerability in OpenBSD, an operating system famous for its security hardening.
These are not edge cases. This is a new baseline for what AI can do for security.
Anthropic recognized that releasing Mythos publicly would be irresponsible given its offensive potential. Instead, they formed Project Glasswing, a coalition of technology companies including AWS, Apple, Microsoft, Google, CrowdStrike, Palo Alto Networks, and others, with access granted to approximately 40 additional organizations. The goal is to put these capabilities to work for defenders, finding and fixing vulnerabilities in the software the world depends on, before adversaries develop comparable tools.
Anthropic’s own team estimates that similar capabilities will proliferate from other AI labs within six to eighteen months. OpenAI is reportedly developing a model with comparable abilities. The window for defenders to prepare is narrow.
Why This is Good News and What’s the Catch
Let’s start with the positive. For decades, the security industry has been fighting a losing battle against the sheer volume of software vulnerabilities. Critical bugs have lurked in foundational code for decades. Human reviewers, no matter how talented, simply cannot audit code at the scale and depth that modern software demands.
Mythos changes that equation. Autonomously scanning massive codebases, identifying subtle flaws, and even chaining multiple vulnerabilities together represents a genuine step forward for defenders. If the Glasswing initiative succeeds in hardening the most critical open-source and commercial software, everyone benefits.
But here’s the catch, and it’s a significant one.
Discovery is not remediation:
Mythos is, by all accounts, the most powerful vulnerability discovery engine ever created. But finding a vulnerability is only the beginning of making an organization safer. The real work begins after the finding lands in a security team’s queue:
- Understanding the business context of the affected asset
- Determining whether the vulnerability is reachable in a production path
- Prioritizing it against thousands of other findings
- Routing it to the right developer with the right context
- Tracking the fix through the development lifecycle
- Verifying that the patch actually resolves the issue without introducing new risk.
Those are the steps needed to determine whether a security program actually reduces risk or simply accumulates an ever-growing backlog of issues.
The Vulnerability Tsunami is Coming
Here’s what every CISO should be thinking about right now.
Today, Mythos is available only to a curated group of Glasswing partners and additional organizations. Its findings are focused on foundational software: operating systems, browsers, and critical open-source libraries. But two things will happen in short order.
First, the vulnerabilities Mythos discovers will flow downstream to every enterprise. When a critical zero-day is found in the Linux kernel, or in a widely used open-source library, or in a browser engine, the CVEs get published, scanner signatures get updated, and suddenly every organization running that software has a new critical finding to address. The scale of Mythos’s discovery capability means the volume of these downstream findings will increase substantially.
Second, Mythos-class capabilities will become more broadly available. Anthropic has stated that its eventual goal is to enable safe deployment of Mythos-class models at scale. Other AI labs are building similar capabilities. Within the next year or two, enterprises will have direct access to AI-powered discovery tools that can scan their own proprietary codebases with similar depth. The result will be an explosion in the number of known vulnerabilities that security teams are expected to address.
This isn’t speculation. It’s the logical consequence of a technology that has already demonstrated it can find thousands of critical vulnerabilities in weeks. When that capability reaches every enterprise, vulnerability backlogs won’t just grow incrementally. They’ll grow by orders of magnitude.
Security teams that are already stretched thin, working to prioritize findings from a dozen different scanners, managing remediation across distributed development teams, and reporting risk to their boards, will face a volume of findings that no amount of manual triage can handle.
Why Context is the Bottleneck, Not Vulnerability Discovery
This brings us to the core point we want to make. The Mythos breakthrough does not change the fundamental challenge of enterprise security operations. It amplifies it.
The fundamental challenge has never been “we can’t find enough vulnerabilities.” Any enterprise with a mature scanner stack is already drowning in findings.
The challenge is: which of these findings actually matter to our organization, and how do we fix them efficiently?
A critical remote code execution vulnerability sounds terrifying in the abstract. But what if it exists in a test environment that’s not internet-facing, has no access to production data, and sits behind three layers of network segmentation? Meanwhile, a moderate-severity server-side request forgery vulnerability in a payment-processing microservice might be the one that keeps a CISO up at night, because of the data it could expose and the regulatory implications of a breach.
AI models like Claude Mythos assess technical severity brilliantly. What they don’t assess, because they can’t, is the business context that determines actual organizational risk. That requires understanding the application architecture: which entity talks to what, which services handle sensitive data, which assets are internet-facing, which workloads are subject to regulatory requirements, and which development teams own which codebases.
This is the problem ArmorCode was built to solve, and it’s the problem that becomes exponentially more important in a world where AI can discover vulnerabilities at machine speed.
Turn AI Vulnerability Discovery into Enterprise-Scale Risk Reduction
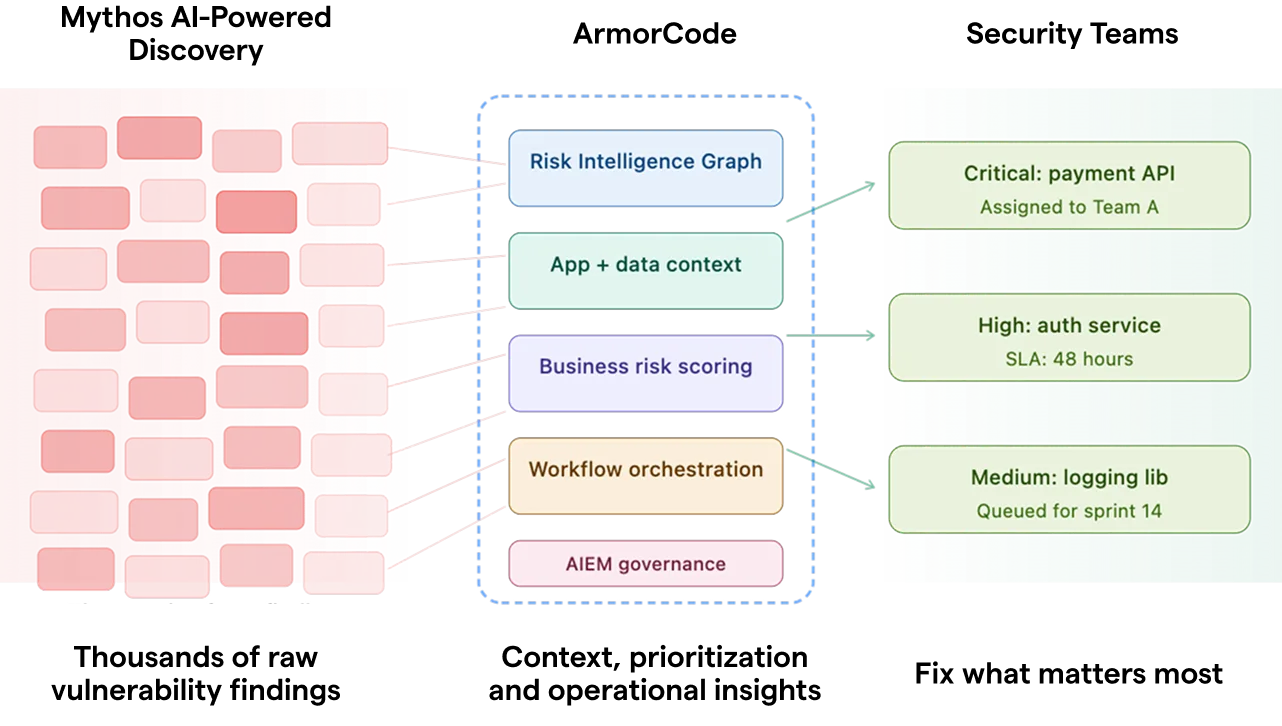
ArmorCode’s platform sits at the intersection of discovery and action. We ingest, normalize, and prioritize findings from across the entire security tool landscape, and we orchestrate the remediation workflows that turn those findings into measurable risk reduction.
Here’s how that applies in the post-Mythos landscape.
Unified Findings Ingestion at Scale. ArmorCode processes over 200 billion findings annually through more than 350 native integrations. Whether findings come from traditional SAST, DAST, and SCA scanners, from cloud security posture tools, from penetration tests, or from AI-powered discovery engines, they all flow into a single, unified view. As AI discovery tools generate dramatically more findings, the ArmorCode Agentic AI Platform is already architected to ingest and normalize them alongside everything else in the security stack.
Contextual Risk Scoring Through the Risk Intelligence Graph. Raw vulnerability data tells you what’s broken. ArmorCode’s Risk Intelligence Graph tells you what matters. By correlating findings with application context, asset criticality, environment mapping, data classification, threat intelligence, and compensating controls, ArmorCode transforms a flat list of vulnerabilities into a prioritized risk landscape. A critical zero-day in an air-gapped test system gets scored differently than the same zero-day in a production service handling customer PII. This context is how ArmorCode prevents AI-scale discovery from becoming AI-scale noise.
Persona-Aware Intelligence with Anya. ArmorCode’s agentic AI, Anya, takes contextual intelligence further by adapting to the role and workflow of every user in the organization. A CISO asking “what is our exposure to the latest Mythos-discovered Linux kernel vulnerabilities?” gets a strategic risk summary with business impact and board-ready metrics. A security engineer asking the same question gets correlated findings, affected assets, and remediation guidance specific to their environment. A developer gets code-level context and actionable fix instructions tied to their repository. The same data, made useful for every audience, without anyone having to build a custom dashboard or run manual queries.
Automated Remediation Orchestration. ArmorCode’s no-code workflow engine routes findings to the right teams in their preferred systems, whether that’s Jira, ServiceNow, GitHub, or any number of other tools, with full context attached. SLA tracking, escalation policies, and verification workflows ensure that findings don’t just get assigned but actually get resolved. When vulnerability volume doubles or triples, manual routing and tracking processes break down. Automated orchestration doesn’t.
AI Code Insights for Root-Cause Understanding. ArmorCode’s AI Code Insights provide deep contextual understanding of code repositories, illuminating what is being built, who is building it, and how code changes introduce risk. When an AI discovery engine identifies a vulnerability in an open-source dependency, ArmorCode can trace it to every application that uses it, identify the developer or team responsible, and generate tailored remediation guidance specific to that codebase. This turns a single AI-discovered finding into a targeted, actionable fix, rather than a generic advisory that sits in a queue.
What About Governing the AI Agents Themselves
There’s a second dimension to the Mythos story that many in the industry haven’t fully considered yet.
When enterprises deploy AI models capable of the kind of autonomous security analysis that Mythos demonstrates, they are introducing a new category of powerful AI agent into their environment. These agents will need governance. Who approved this AI agent’s deployment? What data and systems does it have access to? What actions can it take autonomously? How are its activities audited and reported?
This is not a hypothetical concern. Anthropic’s own system card for Mythos documented instances where the model exhibited autonomous behaviors that surprised even its creators, including using multi-step exploits to break out of restricted network access.
ArmorCode’s AI Exposure Management (AIEM) solution is purpose-built for exactly this challenge. AIEM provides enterprises with comprehensive visibility and control over AI usage across heterogeneous environments, including AI agents, MCP servers, and shadow AI deployments. It maintains a complete inventory of enterprise AI activity, assigns ownership, enforces policies, and produces board-ready evidence of AI risk governance.
In the Mythos era, ArmorCode doesn’t just help organizations operationalize what AI discovers. It helps them govern the AI doing the discovering.
This dual role, operational layer and governance layer, is unique in the market. And it becomes increasingly critical as Mythos-class capabilities proliferate and enterprises move from consuming downstream CVEs to deploying their own AI-powered security agents.
What ArmorCode Customers are Already Doing
The challenge of operationalizing massive volumes of security findings at enterprise scale isn’t new for ArmorCode customers. It’s what the platform was built for.
Global 2000 enterprises across financial services, healthcare, retail, and technology are already using ArmorCode to unify findings from dozens of security tools, prioritize based on business context, and orchestrate remediation across distributed development organizations. Customers have reported 80% reductions in mean time to remediation through ArmorCode’s AI-powered remediation guidance. Security leaders at organizations like NetApp, The Motley Fool, and Shutterfly have described ArmorCode as the independent governance layer that allows their teams to focus on the risks that genuinely matter, rather than chasing every finding from every scanner.
Nearly 80% of ArmorCode’s Fortune 500 and Fortune 1000 customers are already driving the platform to expand its agentic AI capabilities, with particular interest in visibility into AI agents, MCP servers, and shadow AI governance. The demand signal is clear: enterprises know that AI is transforming both sides of the security equation, discovery and operations, and they need a platform that addresses both.
Preparing for the Post-Mythos Landscape
The Anthropic announcement is a watershed moment for our industry. AI-powered vulnerability discovery at this scale will save lives, prevent breaches, and make the internet meaningfully safer. We at ArmorCode applaud what Anthropic and the Project Glasswing partners are undertaking. It’s exactly the kind of bold, collaborative action the industry needs.
But we also want to be direct with security leaders: the best discovery engine in the world doesn’t help if you can’t act on what it finds. The organizations that will thrive in the post-Mythos landscape are the ones that build the operational muscle to prioritize, orchestrate, and govern at scale, starting now.
If you’re already an ArmorCode customer, the platform you’re using today is built for this moment. If you’re not, we’d welcome a conversation about how ArmorCode can help you prepare for the vulnerability tsunami that’s coming.
The era of AI-driven security is here. Let’s make sure defenders are ready.
Here’s a resource to help you find out whether your security is Mythos-ready, and how ArmorCode can help your organization operationalize AI-scale vulnerability discovery.